AlphV Reclaims FBI Seized Onion Site, Escalates Threats
Federal action backfires against one of the most renowned groups on the street.
:tl;dr summary of United States government (and associated entities) vs ALPHV ransomware group
December 10th, 2023:
ALPHV primary domain goes offline, administration saying it is hardware failure December 10th, 2023: Rumors circulate that is it LE taking down ALPHV December 11th, 2023: ALPHV denies allegations
December 19th, 2023, 7:26AM EST: ALPHV domain seized
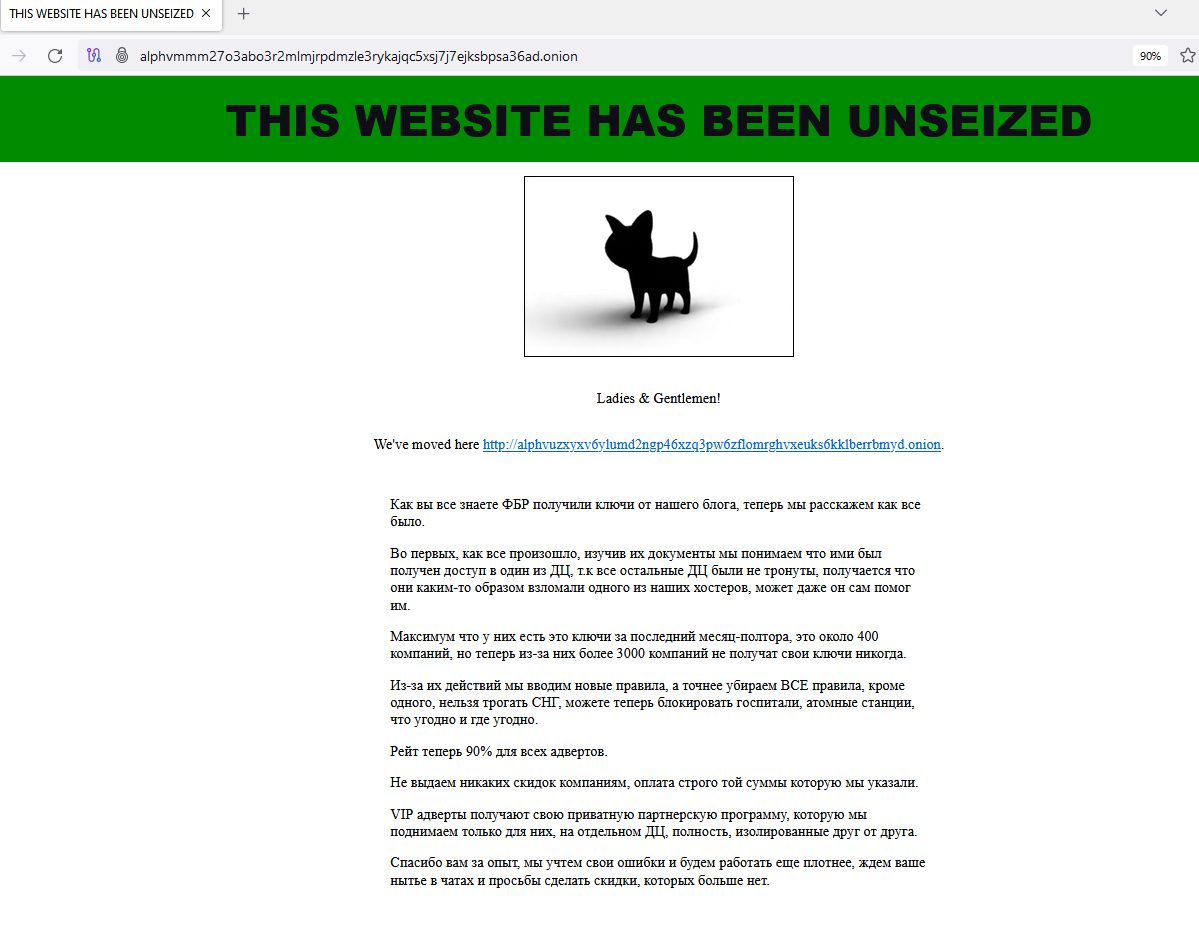
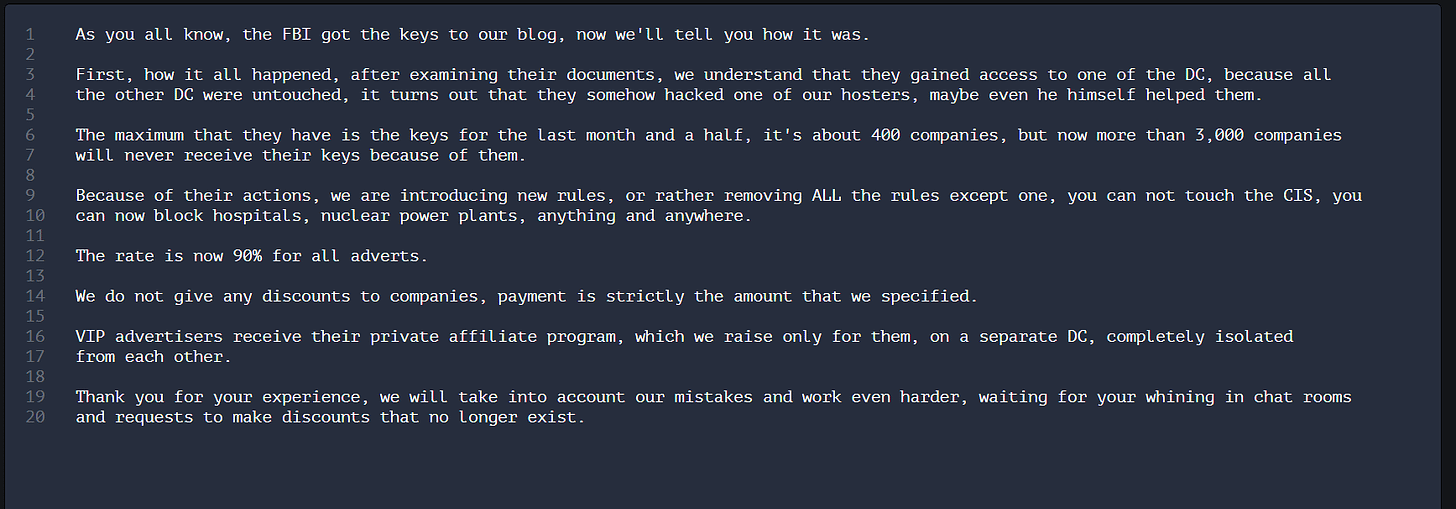
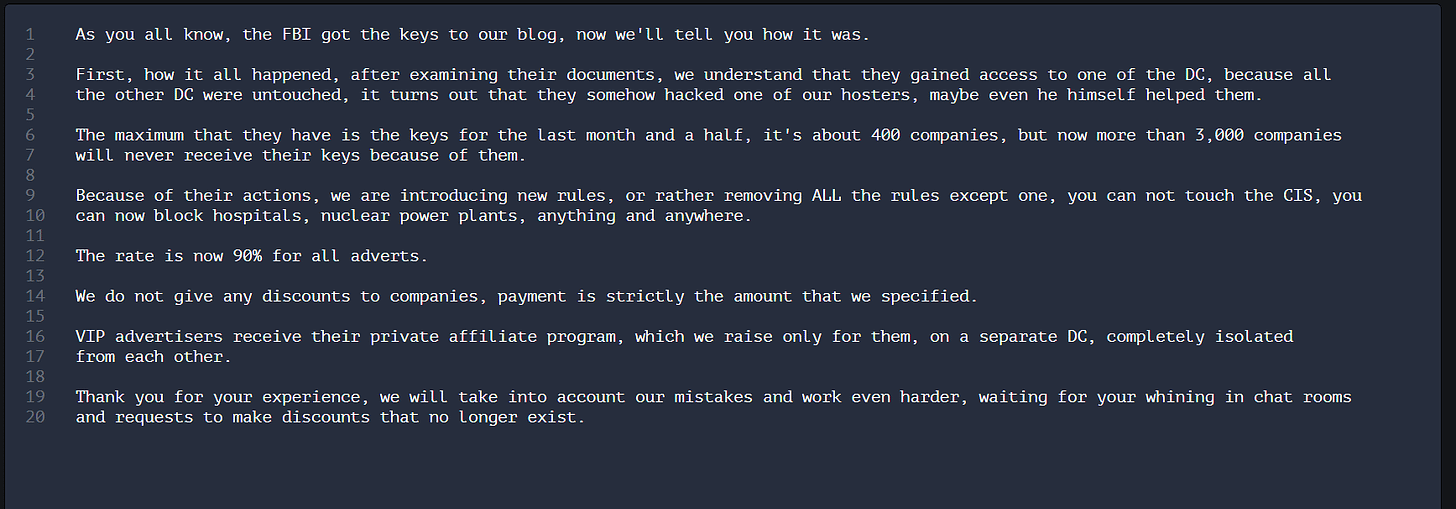
December 19th, 2023, 7:42AM EST: ALPHV states this is the old domain and it doesn't matter
December 19th, 2023, 9:56AM EST, United States Department of Justice releases official statement on the seizure of ALPHV as well as compromising of their servers
December 19th, 2023: 12:34PM EST, ALPHV unseizes domain and threatens retaliation against United States (and associated entities) by allowing attacks against critical infrastructure
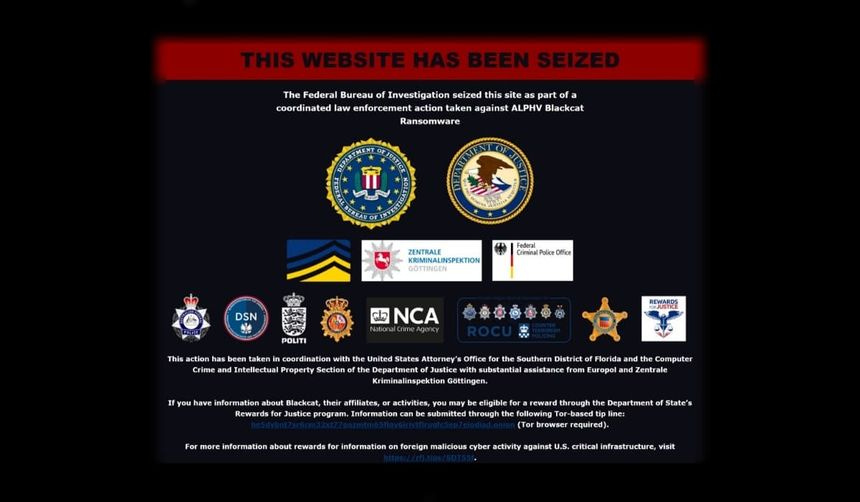
9:00 a.m. PST: An international takedown operation of law enforcement agencies from the United Kingdom, Denmark, Germany, Spain and Australia seized the dark web leak site of the notorious ransomware gang known as ALPHV, or BlackCat.
“The Federal Bureau of Investigation seized this site as part of a coordinated law enforcement action taken against ALPHV Blackcat Ransomware,” a message on the gang’s dark web leak site now read.
In an announcement confirming the disruption, the U.S. Department of Justice said that the international takedown effort, led by the FBI, enabled U.S. authorities to gain visibility into the ransomware group’s computer to seize “several websites” that ALPHV operated.
The FBI also released a decryption tool that has already enabled more than 500 ALPHV ransomware victims to restore their systems. (The government’s search warrant puts the number at 400 victims.) The FBI said it worked with dozens of victims in the United States, saving them from paying ransom demands totaling approximately $68 million
.
The tune quickly changed for law enforcement.
9:30 a.m. PST:
VX-UNDERGROUND:
ALPHV has ... unseized their domain? They claim the FBI compromised one of their domain controllers. Additionally, they state they are removing all rules from their affiliate program (omit the rule on targetting the CIS) - allowing affiliates to target critical infrastructure
One aspect of AlphV operations is its “Ransomware Affiliate Program”. While allowing other threat actors “rent” use of proprietary Blackcat ransomare, perpetuated a splintering attack cycle and misattributed attacks back to AlphV. Previous guidelines preventing these actors from targeting critical infrastructure services (CIS) has now removed, allowing use of this ransomware to be used potentially against hospitals, emergency rooms, energy providers, government databases and numerous other sensitive databases. This aggressive tactic is not unseen for AlphV. Recently, they themselves filed a complaint with the Security and Exchanges Commission, alleging digital lending provider MeridianLink failed to disclose details regarding what the group calls “a significant breach compromising customer data and operational information” - a breach that AlphV took responsibility for. AlphV has ransomware linked to the MGM attacks, attacks on universities, and an attack linked to shutting down the Austrian state of Carinthia, demanding a $5 million ransom to unlock the encrypted computer systems. Besides Covid testing and logistics, it shuttered its internal email portals as well.
An FBI notice in April attributed Blackcat to 60+ affected organizations worldwide.
According to the notice: the group typically uses previously compromised user credentials to gain initial access to the victim system before compromising Active Directory user and administrator accounts after establishing access.
The FBI has re-seized ALPHV's old website, ALPHV would then take it back. It has been seized and then 'unseized' roughly 4 times today. Lockbit ransomware group is now trying to poach ALPHV developers and affiliates