Canada's "NSA" Claims 25% of Global Elections Affected by Russia, China.
FiveEyes countries face increasing vulnerability, according to Canada's Communications Security Establishment. Special focus on Generative AI.
The nature of truth, freedom of conscience, and democratic processes are at stake in the current age of grey zone activity. Due to Canada’s sparse and spread-out population and the present centralization of data, it is among the most connected in the world, and also most vulnerable to online influence. The result of domestic military propaganda campaigns of 2020/21 could leave some to conclude this.
In the meantime, foreign threats are at an all time high while relations with Russia and China are at an all time low. CSE looked at a global dataset and found the number of national elections targeted by some manner of cyber attack has spiked from 10 per cent to 26 per cent since 2015. The agency said those attacks includes attempts to overwhelm the websites of national election agencies and to hack voter information lists.
The report found that rising number of NATO countries and OECD nations have been targeted for electoral interference. Besides Canada’s confiscation of personal Russian oligarch property, the detentions of Huawei’s Meng Wangzhou & Michael Spavor/ Michael Kovrig remains raw in the hearts of both establishments. China has been using the current paradigm to advance interests in academic, domestic, and Arctic surveillance. Both leaders Justin Trudeau and Pierre Poillievre faced WeChat disinformation campaigns in August - September of last year.
While Trudeau maintains power with a parliamentary coalition, its (unlikely) loss of NDP support would trigger a report previous to the next scheduled 2025 election. Activity from both named threats in Russia and China are expected to increase. Therefore if we simply fail to remain aware of impending threats, we willingly surrender our future to those lurking in the shadows of this grey zone. But, as we've always believed, that together, we can prevail against the onslaught of digital manipulation. In a recent report, geared mainly towards its FiveEyes/NATO partners, Canada’s NSA equivalent (as focused on cryptography and foreign SIGINT), the Communications Security Establishment, issued a fairly granulated report based on (mostly) verifiable information. The information missing is the information attributing most of today’s foreign threat activity to specific actors.
State actors have been resorting to smaller “cyber proxies” to fund a lot of activity against hostile countries, while China’s and Iran’s cyber arms are focused on key geographic interests in areas such as Saudi Arabia, Israel, Singapore, Philippines. DDoS and social engineering attacks come out as the most prevalent across the board.
“Identifying the perpetrators of cyber threat activity targeting elections is becoming increasingly difficult as obfuscation techniques and third-party contracting become widespread” -CSE
According to the report, Oxford Internet Institute found 48 instances of states working with influence-for-hire firms from 2019 to 2020, a 128-per-cent increase since the 2017-18 period. CSE also raised the concern towards how artificial intelligence is being used to develop “deep-fake” videos or fake social media profiles to spread disinformation ahead of elections
.
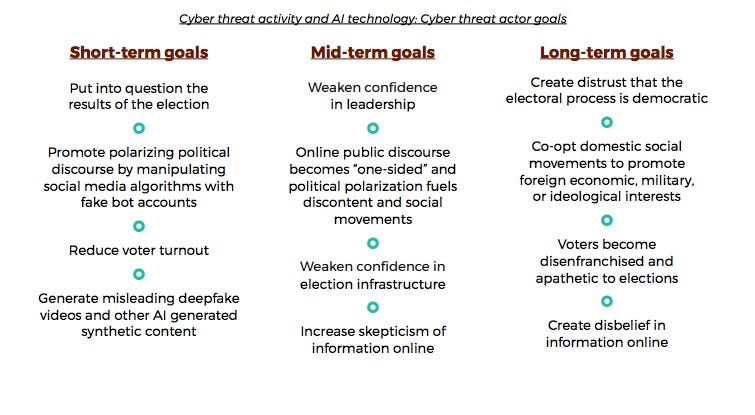
Cyber threat actors are using generative AI technologies to shape the future of democratic debate online. In August 2019, researchers found that there has been an increase in “dark web source activities”, as well as an increase in advertising for custom deepfake services.
“Since the publication of the Cyber Threats to Canada’s Democratic Process: July 2021 update, we have detected an increase in the amount of synthetic content (e.g. deepfakes) relating to elections, almost certainly due to the increased accessibility of many of these technologies. However, we note that the number of reported cases where synthetic content is being used to spread disinformation about elections remains relatively low compared to the amount of synthetic content observed online. We assess that AI synthetic content generation related to national elections will almost certainly increase in the next two years, as this technology becomes more widely available. As synthetic content generation increases and becomes more widespread, it will almost certainly become more difficult to detect, making it harder for Canadians to trust online information about politicians or elections” -CSE
Report Close-Ups:
Cyber Threat Landscape: The report vividly outlines the evolving nature of cyber threats, emphasizing the increased sophistication and frequency of attacks targeting democratic processes.
Disinformation Campaigns: The Centre meticulously dissects disinformation campaigns, highlighting their potential to erode public trust and manipulate electoral outcomes. They swear it's not just the script of a political thriller.
Undermining Public Confidence: The report emphasizes how cyber threats can undermine public confidence in the electoral process, infecting the very core of democracy.
Manipulating Electoral Outcomes: The Centre argues that cyber threats pose a direct threat to fair and legitimate electoral outcomes, stressing the need for robust defensive measures.
Ensuring Electoral Integrity and Cybersecurity: In light of these threats, the report emphasizes the need for robust cybersecurity practices across the nation. It underscores the importance of safeguarding electoral infrastructure, strengthening the resilience of political parties, ensuring transparency in campaign financing, and enhancing cooperation among government agencies, private sector actors, and international partners
.
Protecting Voting Systems: As digital voting systems become more prevalent, the report warns about potential vulnerabilities that could undermine the integrity of elections. While no specific instances of successful hacks have been officially identified, the report cautions about potential future threats. It calls for continuous improvement in secure voting systems, employing technologies such as end-to-end encryption, blockchain, and regularly conducting rigorous penetration testing to identify and address any potential flaws.
Guarding Against Disinformation: To combat the rising influence of disinformation campaigns, a multi-pronged approach is crucial. The report underlines the significance of educating the public about critical thinking and media literacy to enable citizens to discern between fact and fiction. (“Media literacy” in Canada entails focusing on Canada’s content regulator guidelines and its approved/ funded media institutions). It focused further on social media platforms “needing to take more responsibility by tightening policies, increasing transparency, and improving automated detection systems to identify and remove false or manipulative content”.
Cross-Sector Collaboration: The report emphasizes the importance of collaboration between governmental bodies, the private sector, and civil society organizations to effectively manage and respond to these evolving threats. By pooling resources and expertise, these stakeholders can strengthen cybersecurity measures, develop effective incident response plans, and enhance threat intelligence sharing.
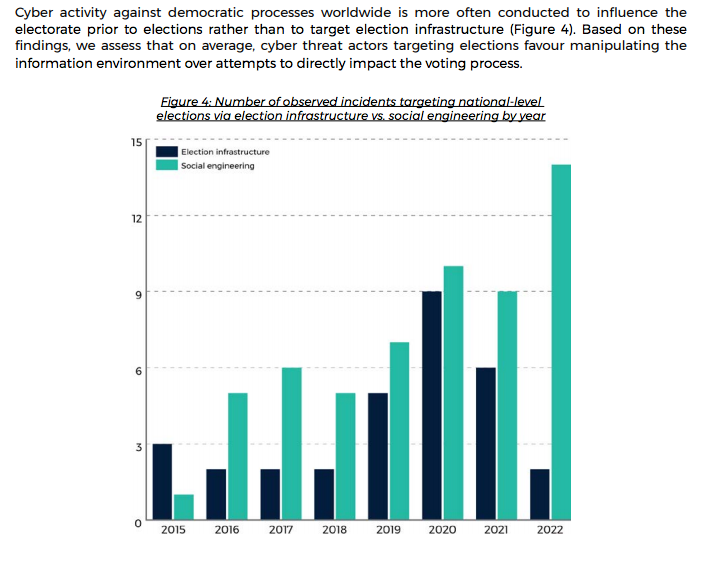
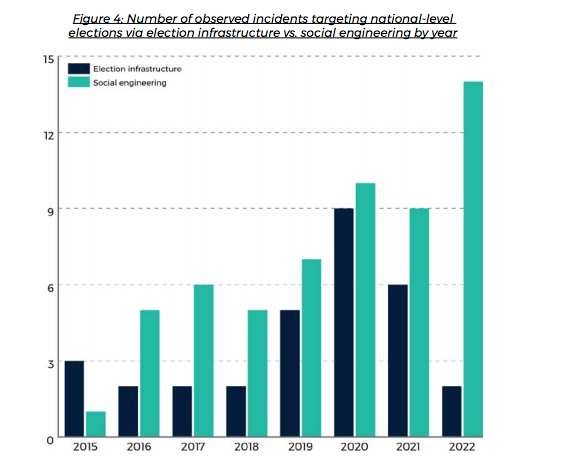
According to the report: “Cyber activity against democratic processes worldwide is more often conducted to influence the electorate prior to elections rather than to target election infrastructure (Figure 4). Based on these findings, we assess that on average, cyber threat actors targeting elections favour manipulating the information environment over attempts to directly impact the voting process”. Social engineering attacks remain the among the most prevalent threats today, comprising a majority of attacks.
There are several reasons why cyber threat actors conduct social engineering rather than target election infrastructure. These include: } having a broader set of targets to choose from } needing fewer bespoke techniques, tactics, and procedures (TTPs) to gain access to privileged information } targeting sources of information that do not have the protection of an IT team (e.g. obtaining information from a political staffer’s personal email account) } justifying hack-and-leaks as being altruistic and providing the public with important information that they “should know about” } being able to outsource influence activities to a marketing or PR firm } having more plausible deniability; targeting the electorate is less direct, and harder to trace”.
Allied Threats:
FiveEyes
United States:
The 2020 U.S. Presidential elections showcased the potential impact of cyberattacks on electoral systems. While the attack did not undermine the final results, it exposed vulnerabilities within the system. Foreign actors, particularly Russia and Iran, attempted to compromise networks, access voter information, and disseminate misinformation. The U.S. remains vigilant against future cyber threats as these incidents highlight the urgent need for robust cybersecurity measures.
Australia:
Although not hit by significant cyberattacks on its electoral system in recent years, Australia has encountered numerous other threats, such as foreign interference and disinformation campaigns. The Australian government has implemented cybersecurity measures and increased cooperation with security agencies to counter potential future threats.
UK:
Besides attacks against municipal infrastructure, health, and election data, these are other significant events compromising “democracy”
Targeting, including spear-phishing, of UK parliamentarians from multiple political parties, from at least 2015 through to this year;
The compromise of UK-US trade documents that were leaked ahead of the 2019 General Election;
The 2018 compromise of the Institute for Statecraft, a UK thinktank whose work “included initiatives to defend democracy against disinformation, and the more recent hack of its founder Christopher Donnelly, whose email account was compromised from December 2021; in both instances documents were subsequently leaked”.
Targeting of universities, journalists, public sector, NGOs and other Civil Society organisations, many of whom play a key role in UK democracy.
New Zealand
New Zealand intelligence officials raised a concern over election integrity leading up to New Zealand’s election’s last October
Andrew Hampton, director general of the New Zealand Government Communications Security Bureau claims the GCSB had witnessed geostrategic competition intensifying around the world, including in the Pacific region over the past year, while serious cyber security incidents continue to threaten New Zealand organisations.
State-sponsored cybersecurity actors feature significantly with 34% of recorded incidents that can be linked to state actors, up from 28% the previous year, said Hampton to Reuters.
Neither agency would name countries involved in the activity but did point to New Zealand’s censure of China for its involvement in a global hacking spree in 2021 and Russia for its malicious cyber activity against Ukraine in 2022.
the threat of foreign interference and espionage is a growing cause for concern, and information is being collected on dissenters of foreign governments and their families being threatened in their home countries.
France:
In France's 2017 Presidential elections, cybersecurity agencies detected an extensive information campaign attempting to undermine candidate Emmanuel Macron by spreading false information. The coordinated hack-and-leak attack targeted his campaign's emails, further amplifying the concerns surrounding the electoral process. France has since implemented measures to address vulnerabilities and safeguard the integrity of their democratic processes.
Germany:
In 2015, the German parliament suffered a cyberattack known as the "Bundestag hack." Believed to be orchestrated by a Russian hacking group known as APT28, this attack resulted in a major data breach compromising sensitive internal information. The incident indicated the potential vulnerabilities of electoral systems to foreign interference, leading to an increased focus on cybersecurity in subsequent elections. The recent Nordstream explosion and deterioration of diplomacy between Germany and Russia from Merkel to Schulz exemplify the pivotal role Germany plays in the region.
Ukraine:
Ukraine has been at the forefront of cyber warfare, experiencing multiple attacks on its electoral systems. In 2014, during the country's presidential elections, the "BlackEnergy" malware disrupted the work of the Central Election Commission and led to outage of electronic voter lists. Subsequent attacks in 2016 targeted the country's power grid and information infrastructure, underlining the sophisticated methods employed by cybercriminals.
Enhancing Cybersecurity:
Governments must strengthen their defenses by investing in robust cybersecurity infrastructure, conducting regular audits, and updating protocols to safeguard critical electoral systems.
Collaborative Efforts: International cooperation among governments, security agencies, and tech companies is crucial in sharing information, expertise, and best practices to counter cyber threats collectively. Collaborative platforms can aid in early detection and rapid response to potential attacks.
Public Awareness: Governments and electoral organizations must educate citizens about the risks of cyberattacks, promoting responsible online behavior, and emphasizing the importance of critical thinking to combat the spread of misinformation.
Securing Supply Chains: Ensuring the security of software and hardware utilized in electoral systems is crucial to prevent cyberattacks that exploit vulnerabilities within the supply chain.
Weakest-link approach: National resilience to cyber attack could be greatly enhanced through an individuals’ own awareness and ability to equip themselves against emerging threats, both digitally and psychologically. It is necessary to ask “Who created this information?” “Who paid for this information?” “Who benefits”? “What role is my digital profile playing in the information landscape”? When the individual citizen is also aware of their vulnerabilities and has the tools to protect their information, the noise of this grey zone activity can be relegated to the background.