CCP Global DNS Probing & Cyber Espionage Shed Light on CERN Worldwide LHC Grid, Academic Networks & NSA/GCHQ Traffic Shaping
China's CERNET mirrors ARPANET, Open Science Grid (OSG), and global computing resources/traffic shaping. GCHQ's Project Tempora, revealed by Snowden, sheds more light on the matter.
Note: This is a two-part article, Part 1 updates China’s cyber-espionage against global governments, focusing on Canada and Southeast Asia. Part 2 focuses on global probing of internet traffic by the CCP, the NSA, and GCHQ.
Part 1:
THERECORD.MEDIA: Dutch military intelligence and security service (MIVD) is warning that a global Chinese cyber-espionage campaign is likely “much more extensive than previously known.”
An alert published on Monday by the country’s National Cyber Security Centre (NCSC) says that the state-sponsored hackers behind the spying operation were exploiting a vulnerability in FortiGate devices for “at least two months before Fortinet announced the vulnerability.”
Chinese nation-state hackers [have also] spent nearly two years targeting a high-level Southeast Asian government department in search of information about the country’s strategy concerning the hotly contested South China Sea.
Researchers from cybersecurity firm Sophos said a 2023 investigation led them to discover three different clusters of hacker activity focused on the same unnamed government organization (likely the Philippines or Malaysia), naming it Operation Crimson Palace.
They initially found a data exfiltration tool used as far back as December 2022 that was previously attributed to the Chinese threat group Mustang Panda but subsequently found multiple clusters of activity that worked in tandem to steal data, acquire credentials allowing for deeper access and more.
Two of the clusters matched tactics and techniques used by the well-known Chinese nation-state group APT15 and a subgroup of APT41 known by some researchers as “Earth Longzhi.”
The researchers found evidence that the groups were using the victim’s network as a sort of “playground” to test different techniques in disabling anti-virus protections or map infrastructure and administrative accounts. Some of the tools used by the attackers had connections to hosts running at other government organizations in the same country that may have also been compromised.
“Furthermore, the target network is a high-profile government organization in a Southeast Asian country known to have repeated conflict with China over territory in the South China Sea,” the researchers said.
China has issued an order, slated to take effect on June 15, that would see its coast guard arrest fishermen if they are caught in waters claimed by Beijing. Philippine President Ferdinand Marcos Jr. called it an “escalation” in comments last week.
POLITICALLY MOTIVATED CYBERATTACKS IN CANADA
Canada’s westernmost province, the significant economic hub of British Columbia’s provincial government network was also compromised, according to provincial premier David Eby. Although the specific nature of the attack has not been clarified, the description of it as “sophisticated” alongside the announcement that it involved government networks would align with espionage from a state-sponsored actor seeking political intelligence.
A suspected state-sponsored hack of government systems in British Columbia, Canada’s westernmost province, is believed to have affected 22 email inboxes containing sensitive information about 19 people, a minister said on Monday.
Mike Farnworth, the province’s public safety minister, told journalists that there was currently “no indication that the general public's information was accessed,” as reported by the country’s public broadcaster CBC.
“We have not identified any misuse of this information or found evidence that the actor accessed specific files,” Farnworth added.
Earlier this week, the Canadian Security Intelligence Service (CSIS) published an annual report including the warning that persistent Chinese interference in Canadian political affairs risked undermining the country’s democracy.
“Canada’s strong democratic institutions, advanced economy, innovative research sectors, and leading academic institutions make Canada an attractive target for cyber-enabled espionage, sabotage, and foreign influenced activities, all of which pose significant threats to Canada’s national security,” the report stated.
The report named China as a state-based threat, warning that its cyber actors “continue widespread cyber espionage against a range of sectors and targets within Canada, including government, academic institutions, private industry and civil society organizations.”
“Canada’s strong democratic institutions, advanced economy, innovative research sectors, and leading academic institutions make Canada an attractive target for cyber-enabled espionage, sabotage, and foreign influenced activities, all of which pose significant threats to Canada’s national security,” the report stated.
GLOBAL DNS PROBING:
Researchers at Bitdefender reported last week that at least eight government and military entities in the South China Sea have been compromised in recent years by a group allegedly aligned with Chinese interests.
Another adversary, named SecShow according to Infoblox security researchers Dr. Renée Burton and Dave Mitchell, operates from the China Education and Research Network (CERNET), a project funded by the Chinese government.
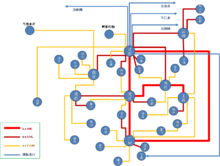
CERNET has a four-layer hierarchy (the nationwide backbone, regional networks, provincial networks and campus networks). CERNET National Center is located in Tsinghua University, which is responsible for operation and management of CERNET backbone nationwide. The ten regional network centers and main nodes are distributed in Tsinghua University, Peking University, Beijing University of Posts and Telecommunications, Shanghai Jiaotong University, Xi'an Jiaotong University, Huazhong University of Science and Technology, South China Institute of Technology, University of Electronic Science and Technology of China, Southeast University and Northeast University, which are responsible for operation, management, planning and construction of CERNET regional backbones.
CERNET provincial nodes are distributed among 38 universities in 36 cities around the country, with persistent access and collaboration with the PLA.
CERNET also has 12 global and regional channels connected with the United States, Canada, the UK, Germany, Japan and Hong Kong. More than 2,000 education and research institutions, 1.2 million PCs and 20 million end users have connected to CERNET
"These probes [originating from CERNET] seek to find and measure DNS responses at open resolvers," they said in a report published last week. "The end goal of the SecShow operations is unknown, but the information that is gathered can be used for malicious activities and is only for the benefit of the actor."
Open resolvers refer to DNS servers that are capable of accepting and resolving domain names recursively for any party on the internet, making them ripe for exploitation by bad actors to initiate distributed denial-of-service (DDoS) attacks such as a DNS amplification attack.
Mapping global networks also opens the possibility of DNS hijacking of any potential vulnerable ports or protocols, potentially on a large scale.SecShow is the second China-linked threat actor after Muddling Meerkat to perform large-scale DNS probing activities on the internet.
"Muddling Meerkat queries are designed to mix into global DNS traffic and [have] remained unnoticed for over four years, while Secshow queries are transparent encodings of IP addresses and measurement information," the researchers said.
CERNET is not the only network of its kind. The infamous ARPANET, now mirrored by the National Science Foundation’s NSFNET. Its architecture is also hierarchical like CERNET, with regional networks connecting to the backbone, which in turn linked to various supercomputing centers and other major hubs. NSFNET played a pivotal role in transitioning the internet from a research tool to a globally interconnected network.

The Worldwide Large Hadron Collider Computing Grid (WLCG), besides sharing computing resources with multiple European academic institutions, also shares resources with the US’ Open Science Grid (OSG). Besides universities of California, Madison-Wisconson, Indiana, Chicago, notable institutions also include Fermilab and Brookhaven National Laboratories, who also conduct research with the US Department of Energy. High-speed fiber optic cables connect the various components of the accelerator complex, including the four main experiments: ATLAS, CMS, ALICE, and LHCb. These experiments produce petabytes of data annually, which are processed and analyzed by a distributed computing grid comprising tens of thousands of servers worldwide.
Each of these institutions, including the WLCG, have their own globally routable IP network ranges, as well as private network ranges. As much as China’s CERNET and Muddling Meerkat is responsible for mapping global DNS traffic, the US has been known to do the same. The CIA’s backdoor inside Swiss encryption software CryptoAG, as well as backdoors in Cisco routers and malware such as FOXACID as revealed by Edward Snowden, can also redirect traffic of target devices, already mapped by the NSA. The NSA also uses a tool called QUANTUMINSERT to track a person’s internet browsing and redirect their computer to one of its FOXACID exploitation servers. This allows the agency to deliver spyware and malware to the targeted individual’s computer.
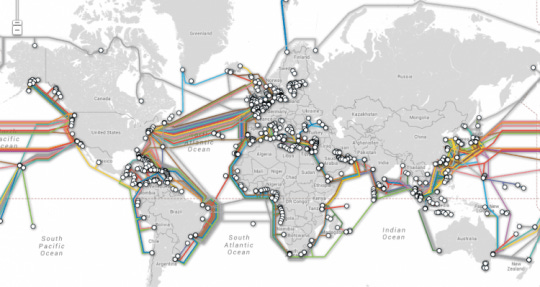
The NSA also uses the term “traffic shaping” to describe any technical means that deliberately reroutes Internet traffic to a location that is better suited, operationally, to surveillance. One technique that allows the NSA/CIA to exploit the global flow of internet data is by tricking internet traffic into traveling through a set and specific route, such as undersea fiber cables that the agency actively monitors according to a leaked top secret document released in 2007.
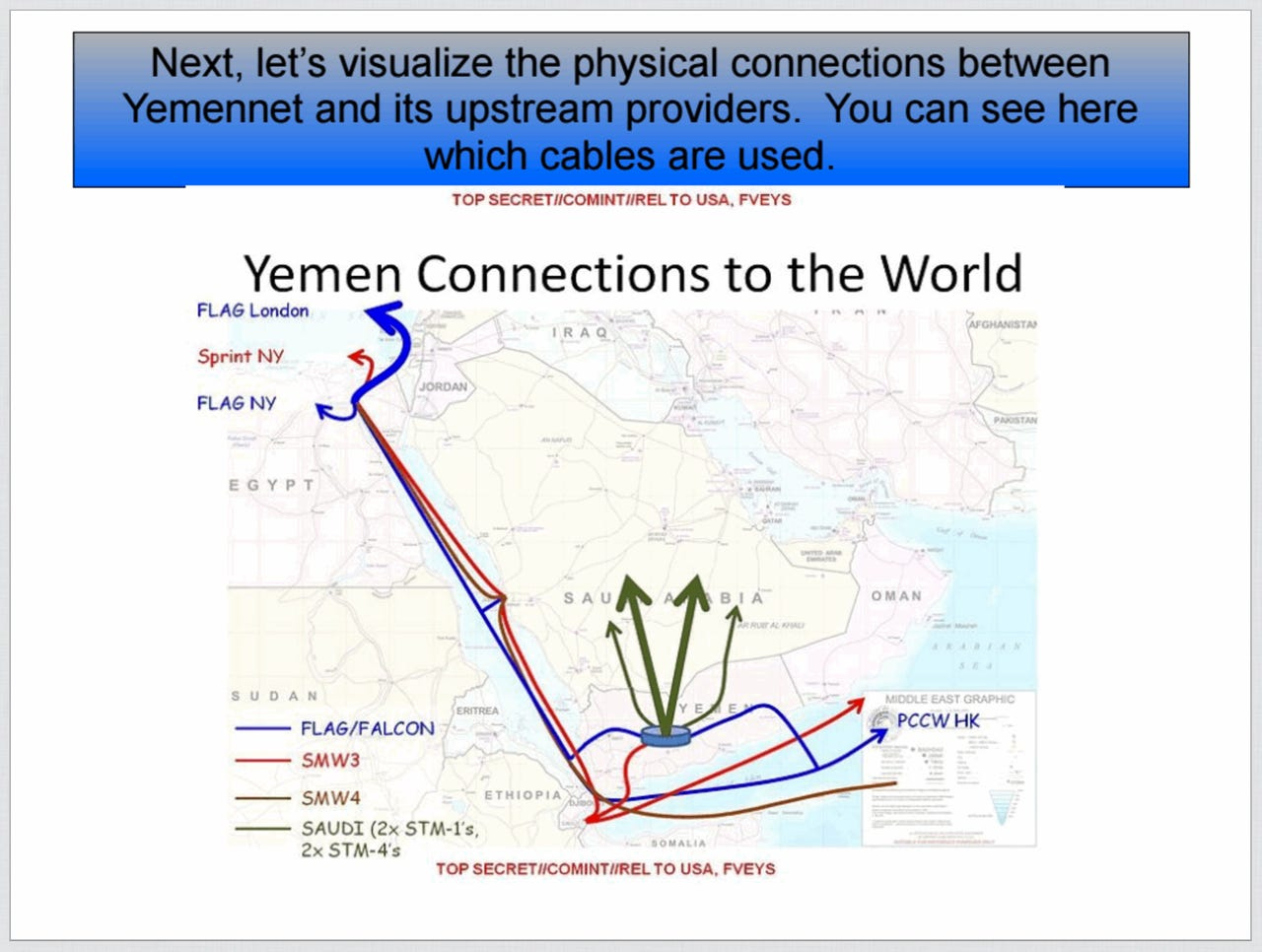
The document's example noted Yemen becaise it is difficult for NSA to passively monitor internet traffic from the cables that run in and out of the country. By shaping the traffic, the agency can trick internet data to pass through undersea cables that are located on friendlier territory.
One NSA document describes how it was able to intercept all domestic inside Yemen to data-centers through Sprint networks, to NSA data centers across 8 US cities. Since it is hard to intercept Yemen’s international communications from inside Yemen itself, the agency might try to “shape” the traffic so that it passes through communications cables located on friendlier territory.
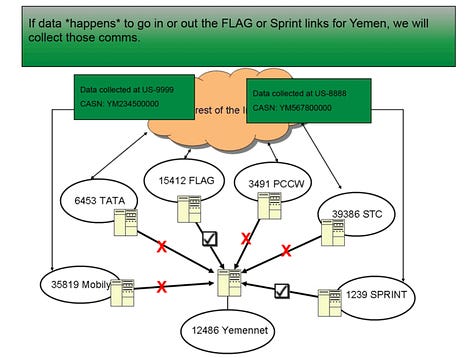
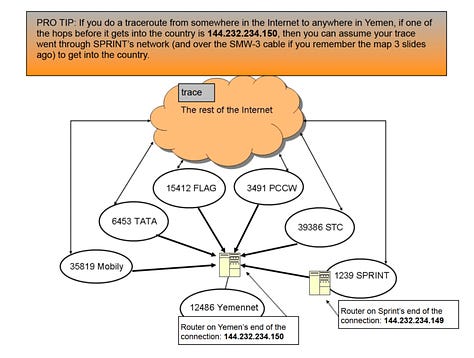
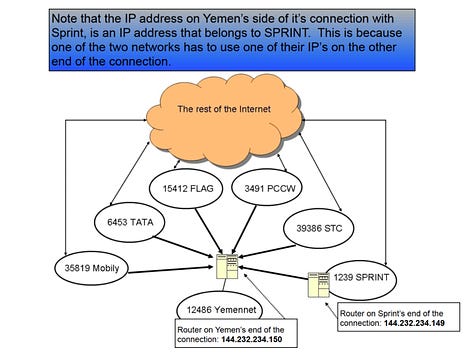
NSA document detailing the technique with Yemen.
SILICONANGLE:
A report in The Atlantic details how British spies are running two rather blatant-sounding programs going by the names of “Global Telecoms Exploitation” and “Mastering the Internet”. The programs are said to be similar to PRISM, and fall under a larger operation called “Project Tempora”. According to documents leaked by Snowden, Tempora gathers up a seemingly ridiculous 21 million gigabytes of data every single day, which is then retained and analyzed for one month.
The Atlantic describes how this data is then shared between Britain’s GCHQ and the NSA, with more than 550 analysts working full time to sift through it all. In this case though, the risk towards our privacy is even greater than anything the NSA collects via PRISM, because tapping into undersea cables means that the agencies can gather the entire contents of communications, rather than just the metadata.
Speaking to security analyst Jacob Appelbaum, Ed Snowden relates how the GCHS is even “worse than” the NSA, because its system vacuums up all data indiscriminately, regardless of who it belongs too or what the content of that data is.
“If you had the choice, you should never send information over British lines or British servers,” stated Snowden.
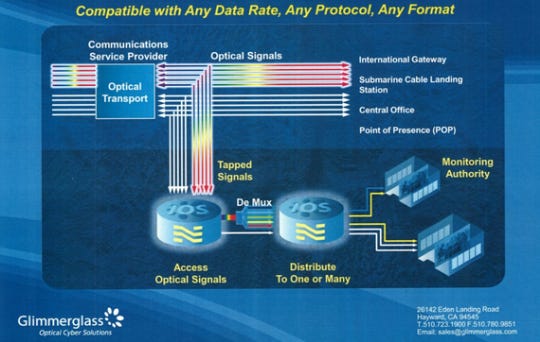
The actual method through which GCHQ captures this data is still a matter of debate, although The Atlantic suggests that it probably involves some kind of “intercept probes” that are installed at various landing stations in the UK. These ‘intercept probes’ are said to be small devices capable of capturing the light sent down a fiber optic cable, bouncing that light around a ‘prism’, copying it, before allowing it to continue on its merry way.
A US government contractor called Glimmerglass is likely to have provided at least some of the technology that allows GCHQ to do this. Aviation Week reported that the company was carrying out similar interceptions on behalf of the US government back in 2010. Further, Glimmerglass has previously boasted of being able to monitor traffic of services including Facebook and Gmail, and is said to have sold its technology to several governments.
“We believe our 3D MEMS technology — as used by governments and various agencies — is involved in the collection of intelligence from … undersea fibers. “We are deployed in several countries that are using it for lawful interception. They’ve passed laws, publicly known, that they will monitor all international traffic for interdiction of any kind of terrorist activity.”
This is all thought to be fairly recent technology however. Previously, the only way that undersea cables could be accessed was by tapping into them directly. To fulfil this purposes, the USS Jimmy Carter submarine was apparently repurposed for the job. The sub apparently accesses the cables at “regeneration points”, where their signal is amplified and where the cables are no longer bundled, but can be accessed individually.
The Federal Intelligence Service (NDB) of Switzerland exchanges information with the NSA regularly, on the basis of a secret agreement to circumvent domestic surveillance restrictions. The NSA has also been granted access to Swiss surveillance facilities in Leuk (canton of Valais) and Herrenschwanden (canton of Bern), which are part of the Swiss surveillance program Onyx.
The Directorate-General for External Security (DGSE) of France also maintains a close relationship with both the NSA and the GCHQ.
In 2011, a formal memorandum for data exchange was signed by the DGSE and the NSA, which facilitated the transfer of millions of metadata records from the DGSE to the NSA.[107] From December 2012 to 8 January 2013, over 70 million metadata records were handed over to the NSA by French intelligence agencie
Having networks mapped by institutions and commercial entities friendly to the Department of Energy and US military and intelligence community, allows intelligence such as China is seeking to gain, to be maintained by the architects of the global internet infrastructure at the NSA and GCHQ.