CyberWar Update: Iran - Israel: IRGC Quds Secret Unit 8030, Albanian Government Targeted (NATO)
Hezbollah Cyber Admin Exposed, Albanian Government Targeted in an Escalation of Grey Zone Activity
From LAB DOKHTEGAN (FORMER GHOSTSEC):
In the past , we exposed the Soori Tech Institute attached to the terrorist Revolutionary Guards Air Forces and their activities. The international agency Iran International also covered this issue in detail. Today, we will expose two of the terrorists of this institution to you:
1. Jafar Khodabakhsh Bonab
- This Haram Laqmeh is one of the Quds forces who works in the weapons production projects for Hezbollah at the TIC Institute.
- The name of the father of this without everything: Muhammad Hossein
- His date of birth is 1985
2. Worthy of character
- He is one of the employees of TIC Institute
- National code: 2240155280 and he was born in 1994
EXPOSED - one of the secret units of IRGC Quds force❗:
Following the disclosure of the 8000 division as the entity responsible for the production and delivery of weapons in the war with Israel, today we are exposing the unit 8030 under division 8000 comprehensively:
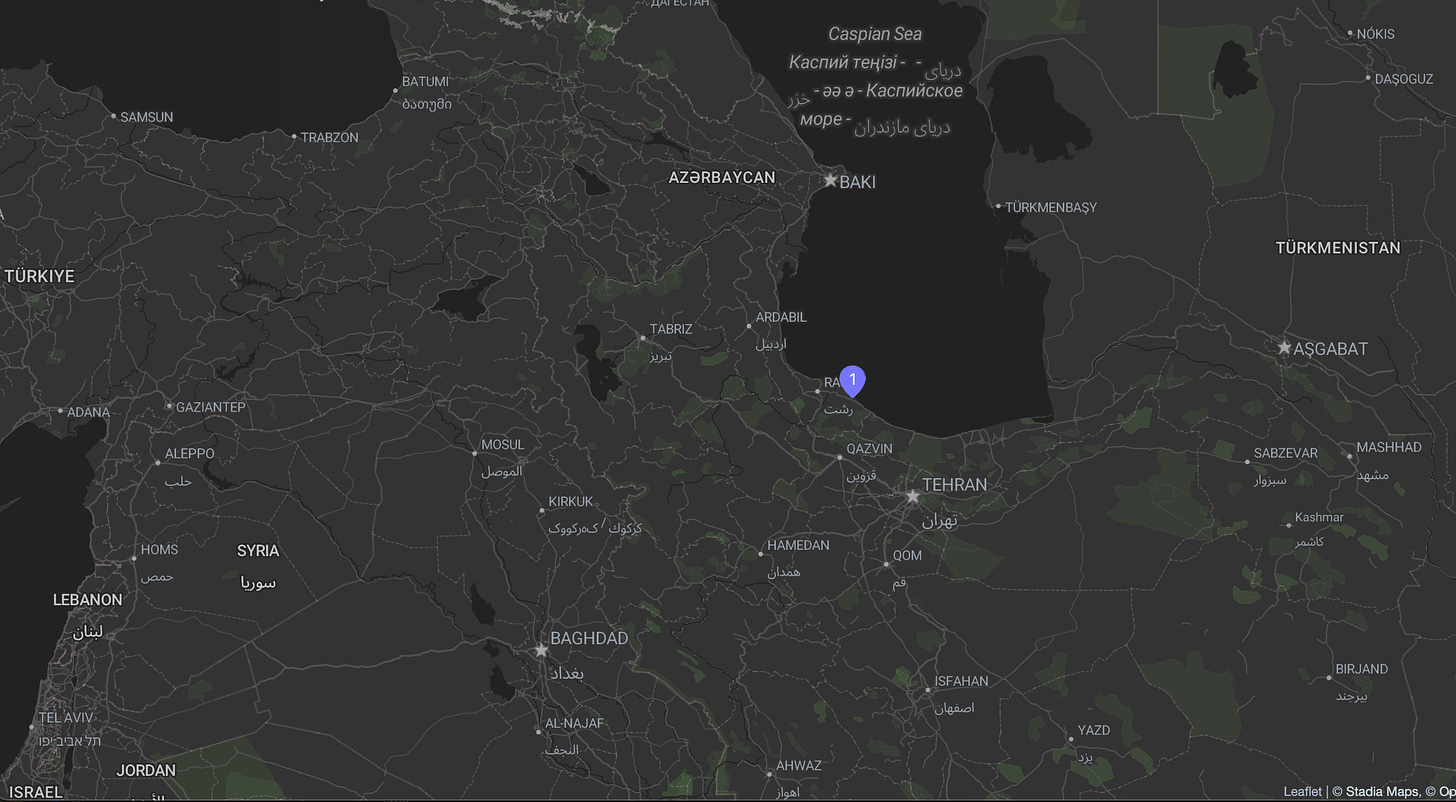
- Unit 8030 is in charge of TIK institute projects.
- Unit 8030 is a naval commando-missile training unit
- The task of this unit is: training in diving, naval commando, sea-based missile and naval drones.
- Unit 8030 is responsible for training Houthi, Lebanese and Palestinian terrorists. These people have been sent to Unit 8030 several times to learn training and equipping courses. These training courses are conducted in the beautiful city of Kenar in Golestan province and in the faculty of the Marine unit of the Islamic Revolutionary Guard Corps named after Imam Khamenei.
- Unit 8030 has several sheds by the sea. These sheds are used for weapons storage and dormitories. In these sheds, marine drone training, diving, shooting, etc. are given.
- Abu Ali Haider is one of the members of Hezbollah who is in charge of dealing with marine projects of unit 8030 in Lebanon.
- In Unit 8030, there are two groups, Noah and Misbah.
- The Commander of Unit 8030 is Ali Khademi, born: 1986, the son of Wali Allah Meibash. His wife's name is Mehbobe Moghdisi and his son is Mohammad Hadi Khademi.
The disclosure of TIC Institute and especially the cooperation of Quds forces with this company will continue. Anyone who has any information about this issue should contact us. Valuable money will be paid for valuable information. All these amounts will be paid in bitcoins to protect the security of our countrymen, and the correspondence will remain very confidential.
CANDLELIGHT CHRISTMAS
On Christmas Day, Israel found itself grappling with widespread power outages and internet blackouts after at least two production units of a major power company collapsed.
Mumblings of Iranian cyberattacks were heard throughout the duration of the blackout.
These claims were refuted without evidence by Meir Spiegler, the CEO of Israel Electric Corporation (IEC)
The initial outage hit 150,000 people throughout the country; however, most of them were reconnected with power grids within hours, with just 34,000 people remaining disconnected.
What caused the blackout?
According to local media reports, the IEC said that alternative units were put into operation as soon as the two units collapsed.
"This break caused loadshedding that caused power outages in a number of locations across the country. Alternative production units went into operation and electricity returned to most of the outages," the IEC stated.
PREDATORY SPARROW - GAS STATION BLACKOUTS WITHIN THE REGIME
The Israel-linked group Predatory Sparrow, or Gonjeshke Darande in Persian, claimed on Monday it was behind a disruption leading to energy blackout affecting 70% of gas stations within the Iranian regime, according to Iranian state TV. Israeli and international media outlets also reported the claim.
“This cyberattack was carried out in a controlled manner to avoid potential damage to emergency services,” Predatory Sparrow said on their X account.
Iran’s civil defence agency, which is responsible for the country’s cybersecurity, said it was still considering all possible causes for the disruptions as it investigated
Iranian state media added that the hacker group has in the past claimed cyberattacks against Iranian petrol stations, rail networks and steel factories.
IRGC CYBER VS. ALBANIA
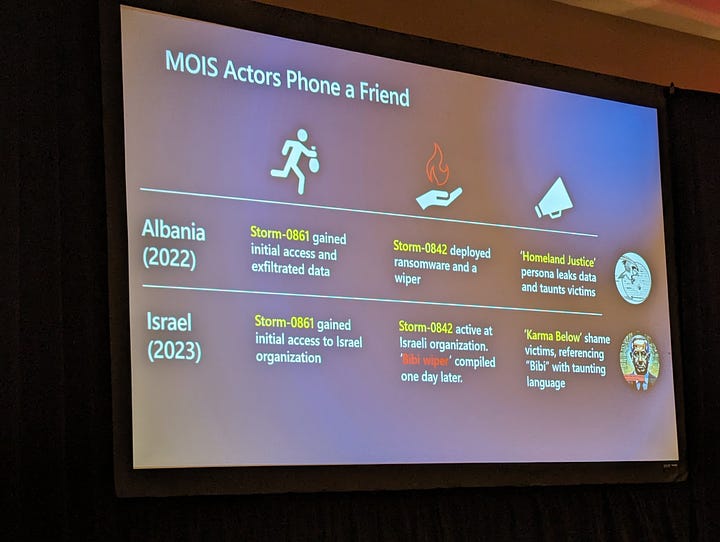
Details surrounding wave of damaging cyberattacks hit Albanian government services in mid-July, with fingers pointed at a threat actor aligned with Iranian interests. According to cybersecurity experts at Mandiant, these attacks represented an expansion of Iran's disruptive cyber operations into new geographic territories.
On July 17, the assault forced Albania's National Agency of Information Society to shut down online public services and government websites temporarily. Mandiant labeled this politically motivated attack as the work of a new ransomware variant called ROADSWEEP. The ransom note accompanying this malware questioned the allocation of taxes toward "DURRES terrorists."
The group HomeLand Justice claimed responsibility for the cyber onslaught, allegedly using a wiper malware alongside ROADSWEEP. Although the specific nature of the wiper remains undisclosed, Mandiant mentioned an Albanian user submitted a sample named ZeroCleare, matching the timeline of the attacks, to a public malware repository on July 19.
ZeroCleare, previously identified by IBM in 2019, targets Windows-based systems, wiping crucial components like the master boot record (MBR) and disk partitions. It's believed to be a collaborative effort among different Iranian nation-state actors, including OilRig.
The attacks also introduced a novel backdoor, CHIMNEYSWEEP, capable of tasks such as taking screenshots, file listing, reverse shell creation, and keylogging. This implant shares code similarities with ROADSWEEP and is distributed alongside faux Microsoft Word documents featuring images of Massoud Rajavi, the former leader of the People's Mojahedin Organization of Iran (MEK).
CHIMNEYSWEEP's origins trace back to 2012, with indications suggesting its previous use in targeting Farsi and Arabic speakers.
Although the cybersecurity firm recently acquired by Google lacked concrete evidence tying these intrusions to a specific adversarial group, they express a moderate belief that individuals supporting Iran's objectives are involved.
These connections to Iran coincide with the timing of the attacks, which occurred just before the World Summit of Free Iran conference, attended by those opposing the Iranian government, notably members of the MEK, near the city of Durres.
Researchers view Iran's potential use of ransomware for politically motivated operations against a NATO member's government websites in the same week as an opposition group's conference as a bold move. They highlighted these findings two months after attributing an attack on a southern U.S. construction company to the Iranian APT group Charming Kitten (Phosphorus).
The malicious overture conducted under the moniker of "ROADSWEEP," a novel ransomware family wielded as a weapon, bearing a note questioning the allocation of taxes to purported "DURRES terrorists." A group styling itself as HomeLand Justice stepped forth, boasting responsibility for this digital affront, claiming not only the use of ransomware but also the deployment of an enigmatic wiper malware.
Adding to the arsenal of cyber artillery was the discovery of "CHIMNEYSWEEP," a previously undisclosed backdoor harboring capabilities to harvest files, capture screenshots, spawn reverse shells, and surreptitiously log keystrokes. Its cryptic origins trace back to the annals of 2012, hinting at a history entwined with attacks aimed at Farsi and Arabic speakers.
Mandiant's elucidation, though lacking direct attribution to a singular adversarial entity, bears the imprint of Iran's orchestration. A narrative woven through the timing of these assaults, strategically coinciding with the World Summit of Free Iran conference, a gathering agitating against the Iranian government, near the Durres port city.
"The use of ransomware to conduct a politically motivated disruptive operation against the government websites and citizen services of a NATO member state in the same week an Iranian opposition groups' conference was set to take place would be a notably brazen operation by Iran-nexus threat actors," the researchers postulated in their calculated assessment.
This revelation, unveiled amidst the digital tapestry, arrives in the wake of Charming Kitten's suspected hand in an assault directed at an undisclosed construction entity in the southern U.S., casting shadows of Iranian APT groups on the global stage of cyber conflict.
Thus, the digital tableau unfolds, revealing a symphony of cyber orchestrations, leaving in its wake the echoes of disruption, geopolitical undercurrents, and the enigmatic dance of technological discord.