IRGC-IO APT42 Impersonates Journalists to Install Custom Backdoors in High-Value Targets
With over 30 operations in 14+ countries, the Iranian Guard Intel Organization subset resorts to social engineering to infect government, education targets with "Nicecurl, Tamecat" malware. (Mandiant)
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.
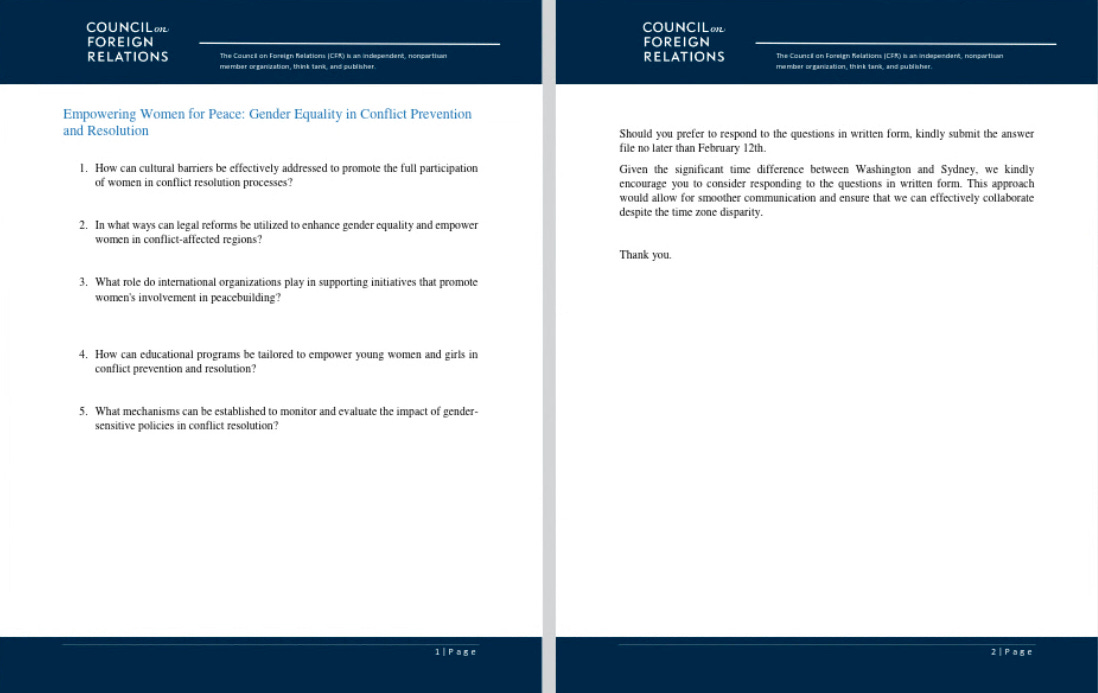
First documented by Mandiant in September of 2022, APT42 - an Iranian nation-state entity - has carried out more than 30 operations in 14 countries. Most recently, the Iran Revolutionary Guard Corps Intelligence Organization (IRGC-IO) subset has resorted to social-engineering attacks, posing as journalists to breach cloud and corporate networks of West-aligned & Middle-Eastern targets. Washington Post, Council of Foreign Relations, The Economist, are among included targets.
NGO’S, media outlets, educational institutes, and legal services have all been among targets observed by the group. Malicious emails are used to infect targets with two custom "Nicecurl" and "Tamecat" backdoors to execute commands and exfiltrate data, according to Google threat analysts following APT42's operations. Both backdoors are deployed via phishing emails with malicious documents, often requiring permissions to run. In their ideal situation, APT42 has cultivated trust with the victim, making this requirement less of a barrier and the victim is more likely to interact with these links. Similar malware was analyzed by Volexity in February, who also tied the threat actors to the IRGC.
The full list of Indicators of Compromise (IoCs) for the recent APT42 campaign and YARA rules for detecting the NICECURL and TAMECAT malware can be found at the end of Google's report.
Objects in the Mirror are Faker Than They Appear.
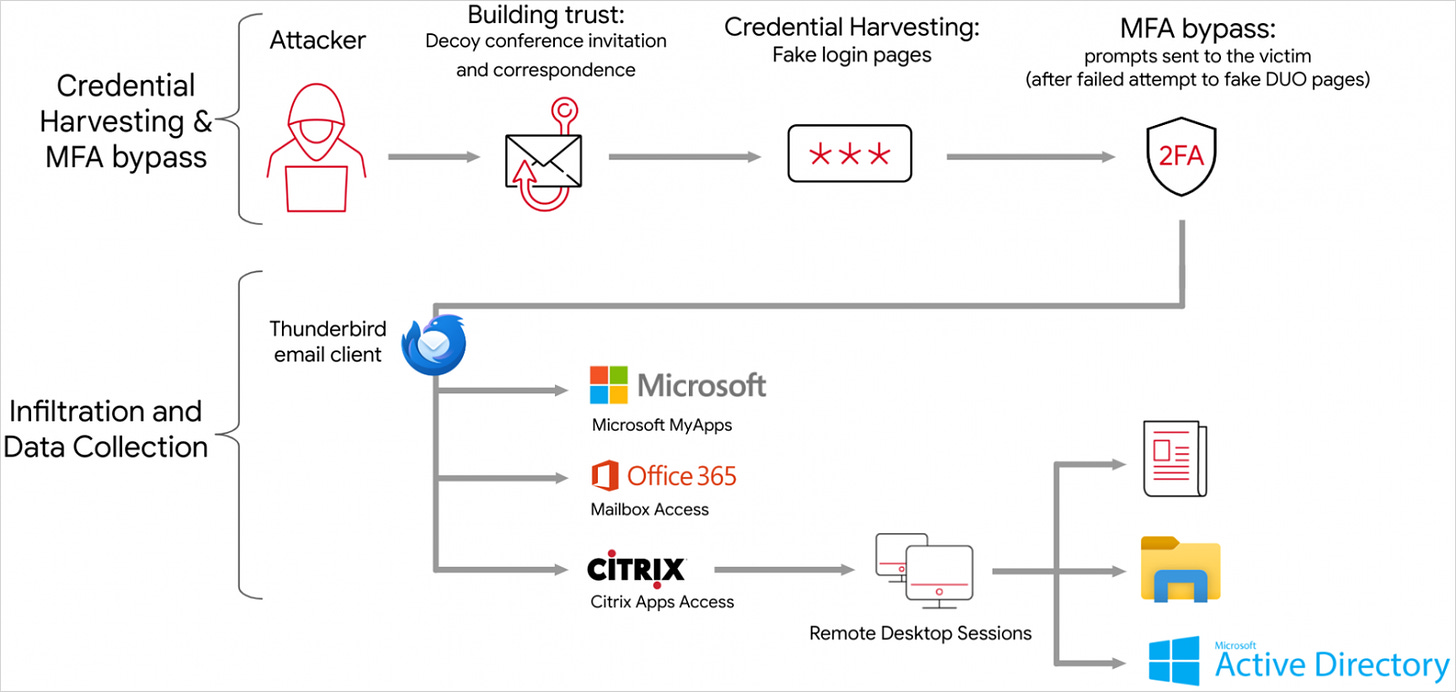
The attack begins with emails from online personas posing as journalists, NGO representatives, or event organizers sent from domains that "typosquat" (use similar URLs) to those of legitimate organizations. These URL’s are usually hosted on Cloudflare domains, Express VPN nodes, and ephemeral VPS servers to make attribution more difficult. APT42 limits its actions to built-in features of the cloud tools it has access to in order to evade detection. It clears its Chrome history after reviewing documents, and uses email addresses that resemble the target organization in order to exfiltrate files to OneDrive accounts.
MANDIANT:
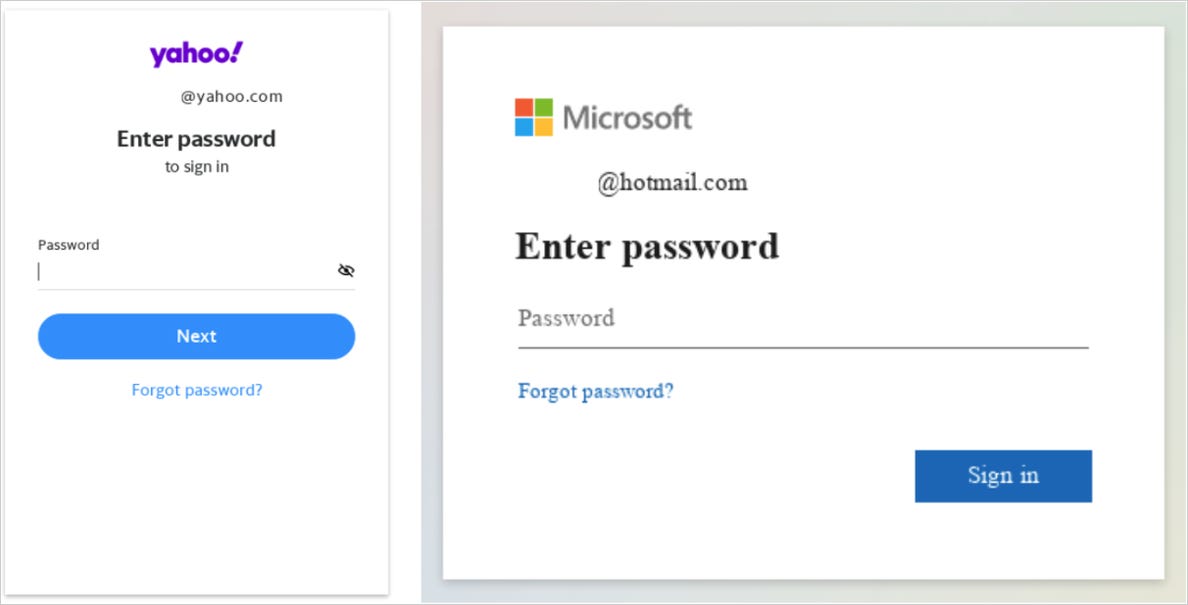
Mandiant observed the use of Javascript files to redirect victims from these links to ultimately serve fake Microsoft 365 login pages.
At least once, Mandiant observed APT42 use several methods—both SharePoint login and fake LinkedIn login pages—to target multiple high-profile personnel of the victim organization during the same campaign.
Washington Post (U.S.), The Economist (UK), The Jerusalem Post (IL), Khaleej Times (UAE), Azadliq (Azerbaijan), are among the included media organizations impersonated by APT42. Mandiant stated that the attacks often use typosquatted domains like "washinqtonpost[.]press".
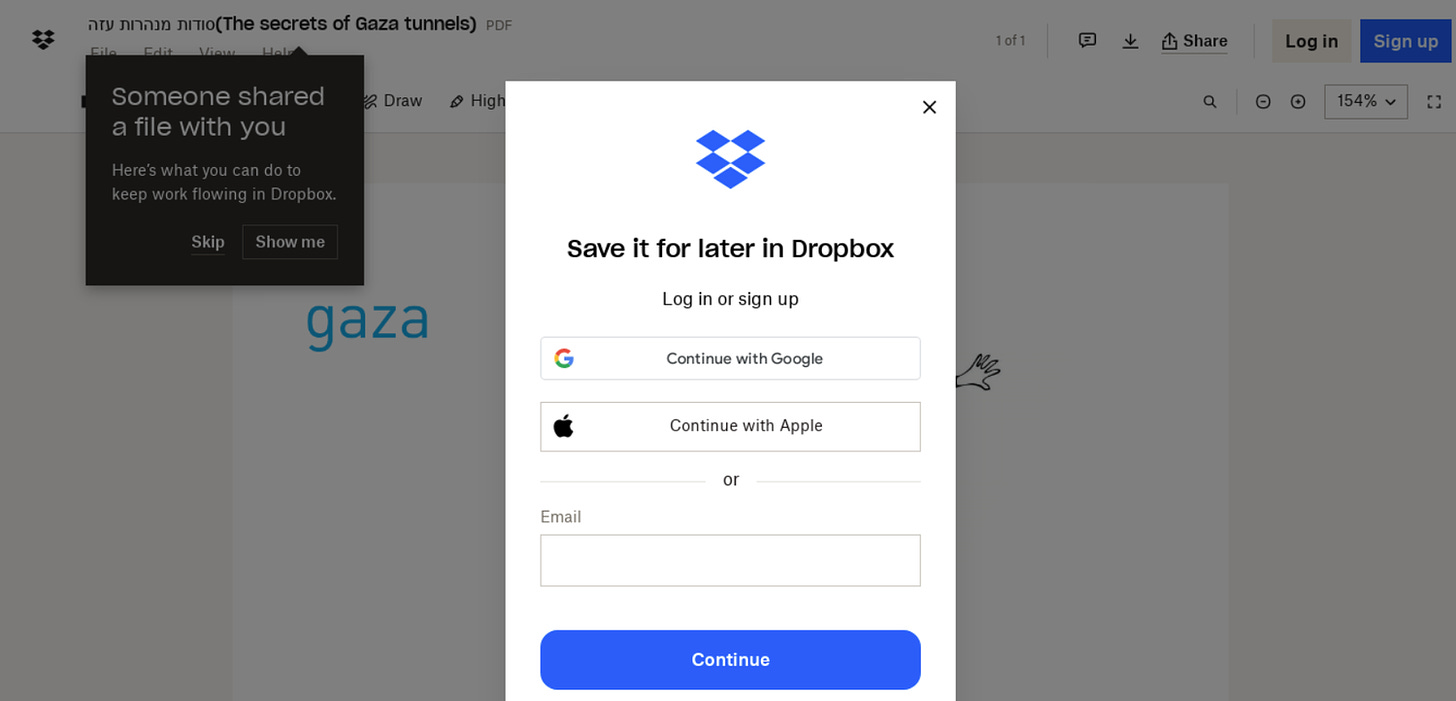
After exchanging enough communication with the target, a malicious URL is sent pertaining to specific “lure topic”.
Clicking on the links directs the targets to fake login pages to trusted platforms like Google or Microsoft, or platforms relevant to the specific field of the targeted professional.
These phishing sites harvest not only the victim's account credentials but also their multi-factor authentication (MFA) tokens. After acquiring the data needed to hijack the target account, the corporate network and cloud environments are cleaned out of sensitive emails and documents.
The motive behind this subterfuge appears to be intelligence gathering, with the attackers likely aiming to infiltrate government agencies, media organizations, think tanks, and other entities of interest. By impersonating journalists, the hackers exploit the trust and curiosity inherent in media interactions to bypass traditional security defenses and gain footholds within target networks.
The implications of this campaign are significant, highlighting the increasingly deceptive tactics employed by nation-state actors to advance their agendas in cyberspace. the exploitation of journalists' identities contributes to a further poisoned- well, low-trust nformation environment, where trust and authenticity are already constantly put to question.