Russian SVR/GRU Groups Elevate Electronic Warfare in Poland, Finland, Serbia While Infiltrating Microsoft, Nuclear Sites
Cozy Bear ,Fancy Bear, Nobelium/ Midnight Blizzard have been busy.
Cyber-warfare has elevated in the Nordic region in the past couple of weeks. Serbia’s energy provider was hacked by ransomware actor Qilin (Chinese for “imminent arrival of a new ruler”), more on that later. The group responsible for the SolarWinds hack : SVR-tied CozyBear, is back, and inside the email accounts of Microsoft’s top executives. Not only have they proven their motive and ability to infiltrate critical infrastructure, they are achieving this against the world’s biggest targets, as well as the world’s most hazardous nuclear site. It was a problem so sensitive and dangerous, employees literally named the incident “Voldemort”.
GUARDIAN: The UK’s most hazardous nuclear site, Sellafield, has been hacked into by cyber groups closely linked to Russia and China, the Guardian can reveal.
The astonishing disclosure and its potential effects have been consistently covered up by senior staff at the vast nuclear waste and decommissioning site, the investigation has found.
The Guardian has discovered that the authorities do not know exactly when the IT systems were first compromised. But sources said breaches were first detected as far back as 2015, when experts realised sleeper malware – software that can lurk and be used to spy or attack systems – had been embedded in Sellafield’s computer networks.
It is still not known if the malware has been eradicated. It may mean some of Sellafield’s most sensitive activities, such as moving radioactive waste, monitoring for leaks of dangerous material and checking for fires, have been compromised.
As the digital curtain has lifted on the SolarWinds hack, the world has witnessed a symphony of deception orchestrated by Russia's elite cyber operatives. Unseen architects infiltrated SolarWinds, injecting a trojan horse into their software updates in 2020. With complete stealth, this backdoor granted the hackers unprecedented access without being notices, compromising government agencies, Fortune 500 companies, and critical infrastructure worldwide. Now, they’re back, and once again targeting an entity at the top of the digital food chain - Microsoft - dancing in harmony with Russian tactics and protocols with other groups conducting their own operations on critical infrastructure.
Cozy Bear, otherwise known as Nobelium or APT 29, emerged as a prime orchestrator of this intricate ballet. In an SEC filing released on Friday, claims were made Russian intelligence group accessed some of the software magnate top executives’ email accounts. Microsoft detected Nobelium, , carried out the attack.
MICROSOFT: The Microsoft security team detected a nation-state attack on our corporate systems on January 12, 2024, and immediately activated our response process to investigate, disrupt malicious activity, mitigate the attack, and deny the threat actor further access. Microsoft has identified the threat actor as Midnight Blizzard, the Russian state-sponsored actor also known as Nobelium. As part of our ongoing commitment to responsible transparency as recently affirmed in our Secure Future Initiative (SFI), we are sharing this update.
Beginning in late November 2023, the threat actor used a password spray attack to compromise a legacy non-production test tenant account and gain a foothold, and then used the account’s permissions to access a very small percentage of Microsoft corporate email accounts, including members of our senior leadership team and employees in our cybersecurity, legal, and other functions, and exfiltrated some emails and attached documents. The investigation indicates they were initially targeting email accounts for information related to Midnight Blizzard itself. We are in the process of notifying employees whose email was accessed.
The attack was not the result of a vulnerability in Microsoft products or services. To date, there is no evidence that the threat actor had any access to customer environments, production systems, source code, or AI systems. We will notify customers if any action is required.
DDoS/Ransomware in Finland
Finnish IT services and enterprise cloud hosting provider Tietoevry has fallen victim to a ransomware attack, impacting cloud hosting customers in one of its data centers in Sweden. The Tietoevry cyberattack occurred during the night of Jan 19-20, affecting services for customers in Sweden. Recovery efforts are underway.
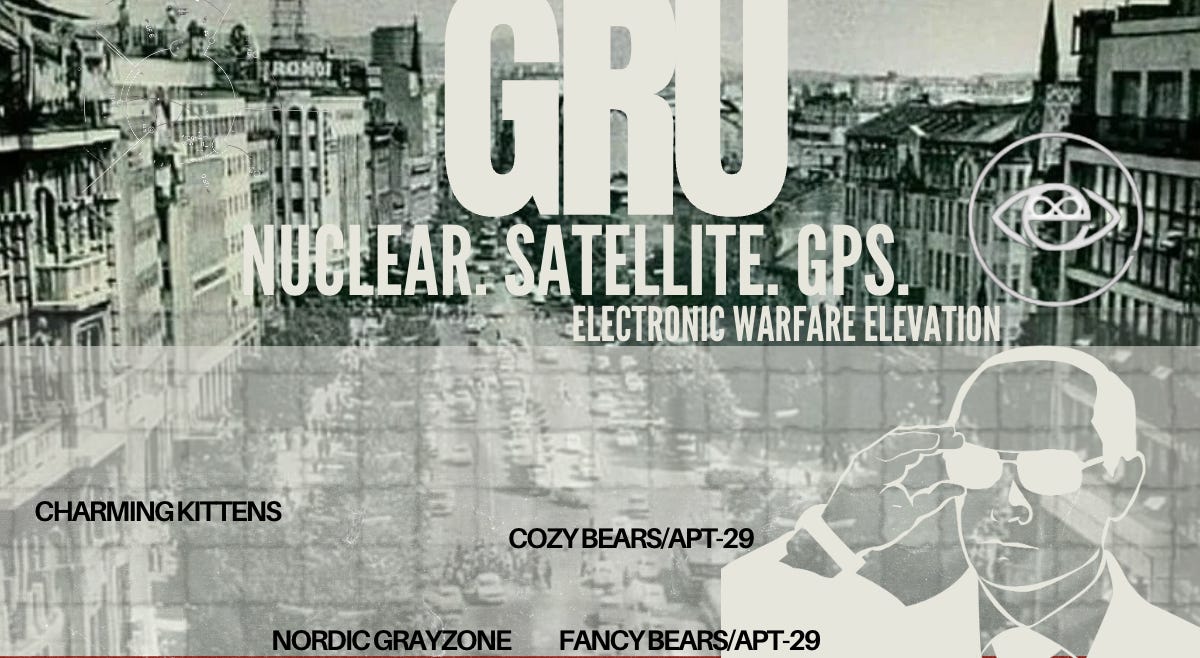
CyberExpress investigated NoName05716 and claims of denial of service and infiltration on their darkweb portal:
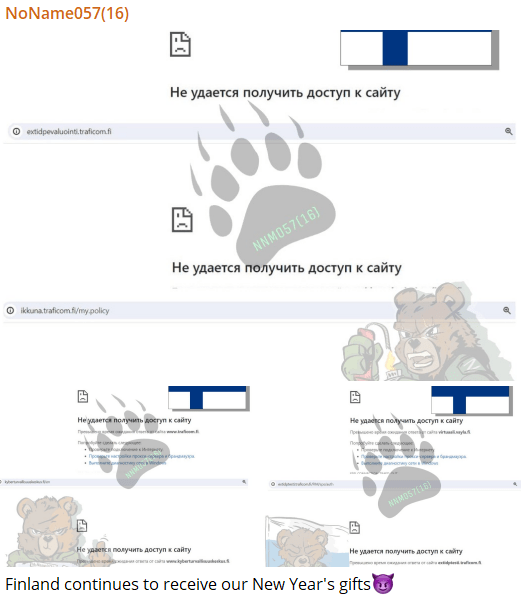
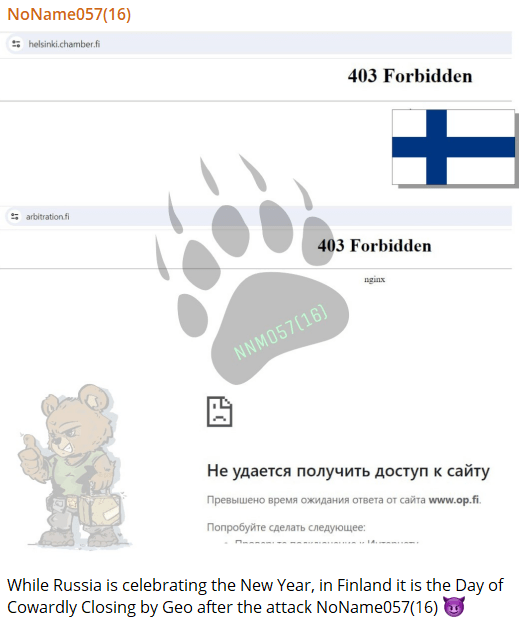
NoName ransomware group, which is also known as NoName057(16) has posted a message on its dark web portal claiming to have targeted the government and private organizations in Finland. The screenshots of the dark web post have been published on the X (formerly Twitter) handle of a cybersecurity research organization.
One screenshot taken from the cybercriminal group’s leak portal reads, “Finland continues to receive our New Year’s gifts (evil smile emoji)”. From what we can understand, this is an attempt to disturb the day-to-day activities of the Finnish citizens as most of the victims of NoName DDoS attacks are government organizations related to road and rail transport as well as cybersecurity.
The screenshot also contains additional information in the Russian language, purportedly linked to the cyberattack. The second screenshot has listed the alleged victims of the NoName DDoS attacks.
The third screenshot taken from the dark web portal of NoName contains a message from the ransomware group directed to the Finnish government. The message reads, “While Russia is celebrating the New Year, in Finland it is the Day of Cowardly Closing by Geo after the attack NoName057(16) (evil smile emoji)”.
DDoS attacks have been on the rise since Russia came to the forefront with the Western powers during the Russia-Ukraine war. Ukraine being backed by the EU and US has irked Russia, which has in turn got multiple EU and US-based organizations being targeted by the Russia-linked hacker groups.
Meanwhile in Poland, more than half of the country dealth with the loss of GPS and satellite communication due to Russia “testing electronic warfare capabilities”
In 2022, Russia conducted a cyberattack against the U.S. telecom company Viasat, which provides internet service in Europe. It also disrupted internet service in Ukraine just before the Russian invasion in February. That attack is one of the most significant digital assaults of the war and lead to a warning from the FBI and CISA about other potential Russian infiltration of satellite systems.
Polish news outlet Radio Zet portal reported "over northern and central Poland, the GPS signal was again jammed”. Warsaw, Łódź, Tricity and Olsztyn were among cities affected , Swedish military intelligence agency MUST is investigating the cause.
Other outlets shared gpsjam.org , showing the extent of GPS problems across much of Poland, with a high level of interference over Kaliningrad, the Russian enclave that borders the country.
CYBERSCOOP: Because the targeted satellite communications provider used the same credentials for “emergency” accounts as ordinary ones, the hackers were able to re-use the stolen credentials for emergency accounts that made it easier for the hackers to move around the system. At the time of the intrusion, the company was also transmitting unencrypted supervisory control and data acquisition, or SCADA, traffic, which can include data like the state of industrial devices and commands from control centers, Emmanuel said.
Unencrypted SCADA data flows are not uncommon, said Aaron Moore, executive leader at cybersecurity firm QuSecure and a former DARPA program manager for satellite programs. Moore said that the majority of SCADA traffic that goes through satellite communications is not end-to-end encrypted and are “steered” though a myriad of routes from the ground site beaming up the information to the satellite and back down to receiving ground site, making this data fairly trivial to intercept.
To improve the industry’s security posture, CISA has argued in the past that space technology should be designated critical infrastructure, which would give the industry greater access to intelligence sharing mechanisms and disaster planning resources.