SANDWORM Strike or Cadet Blizzard? Kyivstar & Ancillary Networks Devastated [UAC-0113/UAC-0165]
Escalated Attack Patterns Imply Two GRU State Actors. “This penetration could lead to eavesdropping, listening to phone calls of our people, reading messages”
[DISCLAIMER: InfiniteEyes attempts to let 48-72 hours pass before reporting on significant events. A major portion of a report is a competing soup of narratives, new information, disinformation. Due to the timing of President Zelenskyy’s visit to US Congress and the current state of the Russia-Ukraine War, it is important to allow attack chains to form and a primary suspect to appear, and report the effects of the fallout]
“The entire perimeter, where all rights are registered, is completely destroyed. Therefore, we need to act on a physical level, connecting conditionally through patch cords to each element of the network, in order to understand the level of destruction at the current time:”
- Kyivstar General Director Oleksandr Komarov
KYIV, UKRAINE: On the morning of Tuesday, December 12, Ukraine Telecoms provider Kyivstar reported its largest cyber-attack seen during the current Russo-Ukraine War. Due to the level of devestation, 75 regional air raid sirens, ATMs, streetlights, and communications. Representatives of PrivatBank and Oschadbank told media outlet Hromadske that part of their ATM machines and card terminals had been affected by the Kyivstar outage. "It’s definitely a state actor,” says a source requiring anonymity, adding that data cable interception showed “a lot of Russian controlled traffic directed at these networks.”
Sources within Kyivstar told several Ukrainian media outlets that hackers breached “a part of the operator's internal systems” and that the company is working to “launch duplicate systems.” The decision to completely shut down the Kyivstar system was made by security forces and the operator in order to "localize" the impact of the attack, one of the sources said. Ukraine has three major telecom operators: Kyivstar, with 24 million subscribers; Vodafone, with 19 million; and Lifecell with 8.5 million.
Switching to another operator in Ukraine is easy — no contract is needed, and it's relatively cheap (a prepaid SIM card costs about $5). In Ukraine's capital, Kyiv, many people were lining up on Tuesday to buy SIM cards from Vodafone and Lifecell to stay connected.
Russian communication services are also under attack. Ukrainian hacktivists are consistently targeting small internet providers in the occupied parts of Ukraine. In June, a group of previously unknown hackers claimed responsibility for a cyberattack on the Russian satellite communications provider Dozor-Teleport, which is used by energy companies and the country's defense and security services.
Most media, including alternative media, are reporting surface level details, using the “serial killer” tactic of not giving publicity to hacker groups, while vaguely blaming “Russian state-actors”. Due to the Russiagate hoax, the false Guccifer DNC hacker accusations, the timing of the current conflict and VIP visit to Congress, it is just responsible journalism to approach this narrative needing more information.
Beyond ransomware actors from Russia, we have seen small DDoS deface campaigns against Ukrainian entities, but rarely an escalated target such as vital telecoms. This requires resources and organization beyond volunteer capabilities. Kyivstar claims to have faced 240 attacks this year alone, however this one made the news for a reason.
Who has the motive and capability to perform this attack? Have these targets been targeted in recent history?
If state-actors are implied, one word should come to mind asking these questions: Sandworm. Another GRU affiliate, Cadet Blizzard.
UAC-0113, a Sandworm-affiliate sponsored by Russia, named by Ukraine’s CERT-UA (Computer Emergency Response Team), has been masquerading as telecom providers, in an attempt to target Ukrainian entities up until last month. The aim is to deliver Colibri Loader and Warzone RAT (Remote Access Trojan) on critical Ukrainian systems. Sandworm has targeted at least eleven Ukrainian internet and telecom providers since May, according to a recent report from Ukrainian cybersecurity authorities that has now been deleted.
The attacks led to service interruptions and potential data breaches one month ago, according to CERT-UA.

SECURITYAFFAIRS: The Sandworm group (aka BlackEnergy, UAC-0082, Iron Viking, Voodoo Bear, and TeleBots) has been active since 2000, it operates under the control of Unit 74455 of the Russian GRU’s Main Center for Special Technologies (GTsST). The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017. In 2022, the Russian APT used multiple wipers in attacks aimed at Ukraine, including AwfulShred, CaddyWiper, HermeticWiper, Industroyer2, IsaacWiper, WhisperGate, Prestige, RansomBoggs, and ZeroWipe. On 19 October 2020, a US-based grand jury released an indictment charging six alleged Unit 74455 officers with cybercrimes. The officers, Yuriy Sergeyevich Andrienko, Sergey Vladimirovich Detistov, Pavel Valeryevich Frolov, Anatoliy Sergeyevich Kovalev, Artem Valeryevich Ochichenko, and Petr Nikolayevich Pliskin, were all individually charged with conspiracy to conduct computer fraud and abuse, conspiracy to commit wire fraud, wire fraud, damaging protected computers, and aggravated identity theft. Five of the six were accused of overtly developing hacking tools, while Ochichenko was accused of participating in spearphishing attacks against the 2018 Winter Olympics and conducting technical reconnaissance on and attempting to hack the official domain of the Parliament of Georgia.
Concurrent with the US indictment announcement, the UK's National Cyber Security Centre (NCSC) published a report which publicly associated Sandworm with the 2018 Winter Olympics attack
Telcos under attack
Researchers from Recorded Future observed a cyber espionage campaign based on a C2 infrastructure, ongoing since August 2022.
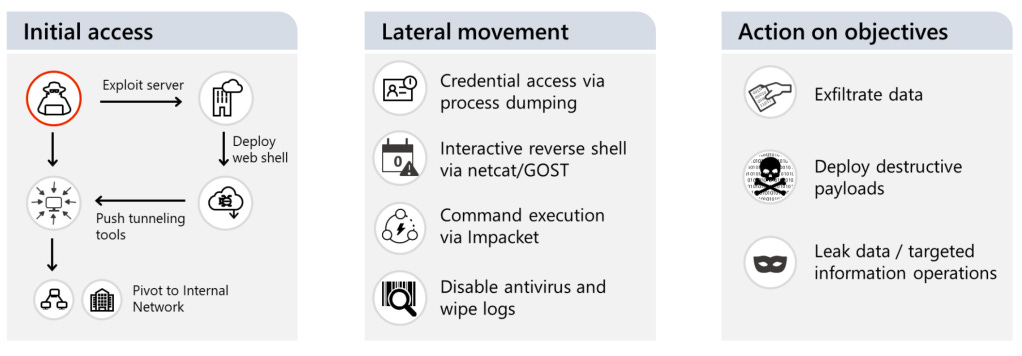
The operators of this recent campaign tracked as UAC-0113, leverage dynamic DNS domains pretending to be Ukrainian telecommunication providers.
Based on the data gathered by CERT-UA, the researchers associated this recent operation with the Sandworm group, establishing a link between the two.
THE RECORD: The infamous Russian state hacking group known as Sandworm has targeted at least eleven Ukrainian internet and telecom providers since May, according to a recent report from Ukrainian cybersecurity authorities.
The attacks led to service interruptions and potential data breaches, said Ukraine’s computer emergency response team, CERT-UA.
Hackers often target telecom providers in both Russia and Ukraine to disrupt communications and internet access amid the ongoing war. Most reported cyberattacks have not caused major shutdowns, and are often resolved within a few hours.
In the recent attacks on Ukrainian telecom providers carried out between May and September, Sandworm used various malware, including and Poseidon to steal credentials and control infected devices, as well as Whitecat to erase any forensic traces.
In addition, the hackers exploited compromised VPN accounts that weren't protected by multi-factor authentication to infiltrate the victims' networks.
The threat actors stole documents, schemes, contracts, and passwords from the targets' official social media accounts in order to make this information public or use it for the promotion of their attacks.
In the final phase of the attack, they disabled active network and server equipment, as well as data storage systems, according to CERT-UA.
In March of last year, Ukraine's major mobile and broadband internet provider, Ukrtelecom, suffered a powerful cyberattack that briefly disrupted its services. The company said it partnered with major cybersecurity firms, including Microsoft, Cisco, Palo Alto, Cloudflare, and ISSP, to prevent future intrusions.
During that same month, another Ukrainian telecom company, Triolan, experienced a cyberattack that reset some of its internal systems.
Russian hackers also targeted several small internet providers, such as Znet, Corbina, Uarnet and Kopiyka.
Ukraine's largest mobile carrier, Kyivstar, reported a massive distributed denial-of-service (DDoS) attack that lasted nearly 30 hours. The company has also faced attacks aimed at stealing users' personal data.
CERT-UA: According to public sources, for the period from 11.05.2023 to 27.09.2023, an organized group of criminals tracked by the identifier UAC-0165 interfered with the information and communication systems (ICS) of no less than 11 telecommunications providers of Ukraine, which, among other things, led to to interruptions in the provision of services to consumers.
The Government Computer Emergency Response Team of Ukraine CERT-UA, in close cooperation with the specialists of one of the providers, took measures to investigate the incident, thanks to which the circumstances of the cyberattacks were established, the characteristic tactics, techniques and procedures of the attackers were clarified, and the malicious intent regarding implementation of cyber threats at a number of similar enterprises.
In the conditions of relentless digitization of a significant number of spheres of modern life, taking into account the persistent threat of loss of communication as a result of kinetic attacks on telecommunications and energy supply facilities, the sustainable functioning of operators and providers is a socially important need.

Another GRU affiliate, dubbed Cadet Blizzard by Microsoft, is another likely suspect. Cadet Blizzard’s activity includes attacks around the world with a particular focus on government services, law enforcement, nonprofits/NGOs, IT service providers and emergency services, according to Microsoft researchers. “The group has consistently targeted IT and software providers", the researchers added, given that one successful attack can lead to multiple downstream compromises just as we see here.
“Unlike other Russian-affiliated groups that historically prefer to remain undetected to perform espionage, the result of at least some notable Cadet Blizzard operations are extremely disruptive and are almost certainly intended to be public signals to their targets to achieve the larger objective of destruction, disruption, and possibly, intimidation”
CYBERSCOOP: Microsoft characterizes the group as a conventional network operator that works without bespoke malware or tooling. “Unlike other Russian-affiliated groups that historically prefer to remain undetected to perform espionage, the result of at least some notable Cadet Blizzard operations are extremely disruptive and are almost certainly intended to be public signals to their targets to achieve the larger objective of destruction, disruption, and possibly, intimidation,” the researchers noted.
Blizzard’s activity overlaps with other cyber operations that “may have a broader scope or a nexus outside of Russia,” including connections to a group Microsoft tracks as Storm-0587, denoting an unattributed activity. That group is linked to malware known as SaintBot, a downloader that can be configured to deliver nearly any other payload. Cadet Blizzard also has support from “at least one private sector enabler organization within Russia,” the researchers noted.
The group uses a hacktivist front called “Free Civilian” to publish and share stolen data, according to the report. Free Civilian posted and leaked stolen Ukrainian government data from various sources on its website in January 2022 ahead of the invasion. The organizations whose data was leaked “strongly correlated to multiple Cadet Blizzard compromises earlier in 2022,” the researchers said, suggesting “that this forum is almost certainly linked to Cadet Blizzard.”